This is an old revision of the document!
Why moodLearning-hosted Site?
Security
At moodLearning we take security seriously. If you don't take it as seriously as we do,
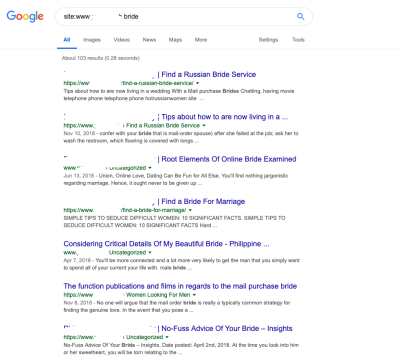
- your site could be an unwitting accessory to crimes. See example of the search engine results for a compromised site with nefarious contents uploaded by a “hacker”
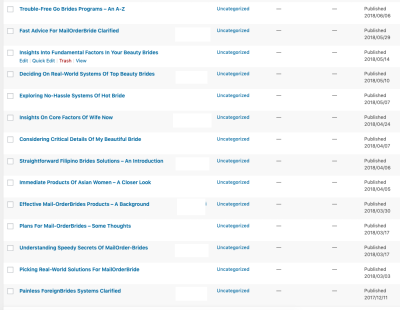
On your end, you may not even notice the “hacking” if you don't pay close attention to it. On your dashboard, the pages have been published by “you”:
* your site could be open for exploitation. This is a sample scanning result from an insecure site:
PORT STATE SERVICE VERSION
21/tcp open ftp Pure-FTPd
22/tcp filtered ssh
26/tcp open smtp Exim smtpd 4.91
53/tcp open domain ISC BIND 9.8.2rc1 (RedHat Enterprise Linux 6)
80/tcp open http nginx 1.14.1
110/tcp open pop3 Dovecot pop3d
135/tcp filtered msrpc
139/tcp filtered netbios-ssn
143/tcp open imap Dovecot imapd
443/tcp open ssl/http nginx 1.14.1
445/tcp filtered microsoft-ds
465/tcp open ssl/smtp Exim smtpd 4.91
587/tcp open smtp Exim smtpd 4.91
993/tcp open ssl/imap Dovecot imapd
995/tcp open ssl/pop3 Dovecot pop3d
2222/tcp open ssh OpenSSH 5.3 (protocol 2.0)
3306/tcp open mysql MySQL 5.6.41-84.1
8080/tcp open http nginx 1.14.1
8443/tcp open ssl/http nginx 1.14.1
Service Info: Host: <redacted info>; OS: Linux; CPE: cpe:/o:redhat:enterprise_linux:6
A number of ports here are open unnecessarily. For instance, Port 3306 is the open database port that can theoretically be exploited to inject unwanted contents to the site or, worse, the database can be erased altogether.